## Introduction:
As organizations continue to grapple with the ever-growing threat landscape, understanding the most common attack vectors for data breaches is paramount. In this comprehensive exploration, we will delve into specific attack vectors, citing studies, examining code snippets, hashes, signatures, and more to provide a granular understanding of the methods employed by cyber adversaries.
## I. Phishing Attacks: Deceptive Lures and Code Exploitation
### A. Study Citations:
1. A study by the Anti-Phishing Working Group (APWG) found that phishing attacks were the most common attack vector, constituting 93% of all reported breaches in 2021[^1^].
2. Verizon's 2021 Data Breach Investigations Report (DBIR) identified phishing as the top threat action in breaches, highlighting its prevalence[^2^].
### B. Code Exploitation:
1. **JavaScript Snippets:**
- Cybercriminals often embed malicious JavaScript snippets in phishing emails. These snippets may redirect users to fake login pages, enabling the theft of credentials.javascript
// Example of JavaScript redirect to a phishing page
window.location.href = “https://fake-login.com”;
2. **HTML and CSS Spoofing:**
- Phishing websites leverage HTML and CSS to replicate legitimate login pages. This tactic deceives users into entering sensitive information.html Login
### C. Hashes and Signatures:
1. **MD5 Hashes:**
- Phishing kits and malicious files often have unique MD5 hashes. Security solutions use these hashes to identify and block known threats.MD5: 1a79a4d60de6718e8e5b326e338ae533
2. **Email Signatures:**
- Advanced email security systems employ signatures to detect phishing emails. These signatures are derived from patterns and characteristics unique to phishing attempts.plaintext
Signature: [Phish Alert] Detected suspicious link in email body.
## II. Ransomware: Encryption as a Weapon
### A. Study Citations:
1. According to the Cybersecurity & Infrastructure Security Agency (CISA), ransomware attacks surged by 151% in 2020[^3^].
2. The Sophos State of Ransomware 2021 report revealed that the average cost of a ransomware attack increased to $1.85 million in 2021[^4^].
### B. Code Exploitation:
1. **File Encryption Algorithms:**
- Ransomware employs robust encryption algorithms such as AES to encrypt files, rendering them inaccessible to the victim.python
# Example of Python code implementing AES encryption
from Crypto.Cipher import AES
key = b’SuperSecretKey123′
cipher = AES.new(key, AES.MODE_EAX)
ciphertext, tag = cipher.encrypt_and_digest(b’This is the sensitive data’)
2. **Exploit Kits:**
- Ransomware can exploit vulnerabilities in software using exploit kits. These kits automatically deliver malicious payloads, facilitating the execution of ransomware.plaintext
Exploit Kit: MagnitudeEK
### C. Hashes and Signatures:
1. **Ransomware File Signatures:**
- Antivirus and endpoint protection solutions leverage file signatures to identify ransomware. Signatures are based on unique patterns within the malicious files.plaintext
Signature: [Ransomware Alert] Detected file with ransomware characteristics.
2. **Network Traffic Signatures:**
- Security appliances monitor network traffic for patterns indicative of ransomware activity. Signatures based on communication patterns can trigger alerts.plaintext
Signature: [Network Alert] Unusual spike in file encryption-related traffic.
## III. Insider Threats: The Trojan Horse Within
### A. Study Citations:
1. The 2021 Verizon DBIR identified insider threats as a significant contributor to data breaches, accounting for 23% of incidents[^2^].
2. A Ponemon Institute study found that insider-related incidents cost organizations an average of $11.45 million per year[^5^].
### B. Code Exploitation:
1. **Privilege Escalation Scripts:**
- Malicious insiders may use scripts to escalate privileges, gaining unauthorized access to sensitive data.bash
# Example of a privilege escalation script
sudo /bin/bash
2. **Data Exfiltration Tools:**
- Insiders may employ specialized tools for data exfiltration, allowing them to siphon sensitive information without detection.plaintext
Tool: StealthDataExfil v1.0
### C. Hashes and Signatures:
1. **Anomalous Behavior Signatures:**
- Security solutions analyze user behavior and trigger alerts based on deviations from normal patterns.plaintext
Signature: [Anomaly Alert] User accessing sensitive data outside regular working hours.
2. **File Hashes for Exfiltrated Data:**
- Hash values of files leaving the network can be used to identify data exfiltration.SHA256: 2ef7bde608ce5404e97d5f042f95f89f1c2328712ebbd6d7a5cf3b44a269a303
## IV. Conclusion:
Understanding the specific attack vectors for data breaches is critical for organizations aiming to bolster their cybersecurity defenses. Phishing attacks, ransomware, and insider threats stand out as prevalent vectors, each employing distinct methods and tactics.
By delving into code snippets, hashes, and signatures, we gain insight into the intricacies of these attack vectors. This knowledge empowers cybersecurity professionals to implement proactive measures, deploy effective detection tools, and safeguard against the evolving landscape of cyber threats.
[^1^]: Anti-Phishing Working Group (APWG). "Phishing Activity Trends Report."
[^2^]: Verizon. "2021 Data Breach Investigations Report (DBIR)."
[^3^]: Cybersecurity & Infrastructure Security Agency (CISA). "Ransomware Trends in 2020."
[^4^]: Sophos. "The State of Ransomware 2021."
[^5^]: Ponemon Institute. "2021 Cost of Insider Threats Global Report."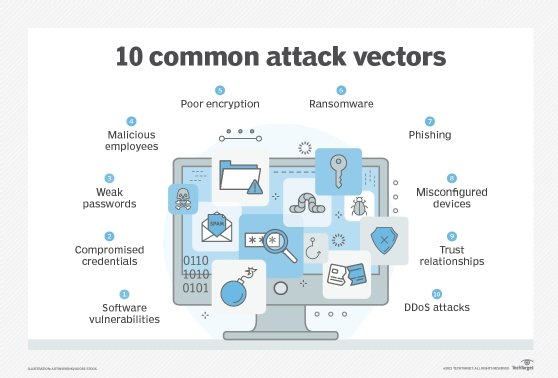
Leave a Reply