This article is a deep dive into the juggle between top password manager free trials vs the actually bedrock trustworthiness of the tech being used beneath the surface.
The lastpass breach should serve as a lesson to everyone of the historical cybersec lesson of this – defenders need to be right all the time, attackers only need to be right once. And by attackers, this means largely bruteforcers, etc.
In the ever-expanding digital landscape, where threats to online security loom large, password managers stand as the unsung heroes, fortifying our defenses against potential breaches. This extensive article embarks on a comprehensive exploration, delving into the intricate details of encryption methods, key management strategies, and security features employed not only by LastPass, Dashlane, and 1Password but also by Bitwarden, Keeper, and NordPass. Our journey doesn’t merely scratch the surface; it’s a deep dive into the historical roots, technological benchmarks, and creators behind these digital fortresses.

I. The Crucial Role of Technology in Password Management:
At the core of any password manager lies a sophisticated array of technologies designed to safeguard sensitive user data. This section navigates through the intricate tapestry of encryption, key management, and other technological facets that serve as the foundation for these security bastions.
II. Encryption Technologies in Password Managers:
- LastPass:
- Fortress of AES-256 Bit Encryption: LastPass boasts a fortress built on the unyielding AES-256 bit encryption, a cryptographic giant with historical significance. The Advanced Encryption Standard (AES) emerged from a competition initiated by the National Institute of Standards and Technology (NIST) in 1997. Belgian cryptographers Vincent Rijmen and Joan Daemen created the Rijndael cipher, which later became AES. This historical context forms the backdrop for LastPass’s choice, placing it at the forefront of cryptographic strength.
- Dashlane:
- The Argon2 Arsenal: Dashlane’s arsenal includes the Argon2 algorithm, a cutting-edge weapon in the fight against brute force attacks. The historical context of Argon2 involves its selection as the winner of the Password Hashing Competition (PHC) in 2015. Developed by Alex Biryukov, Daniel Dinu, and Dmitry Khovratovich, Argon2 represents a collaborative effort to enhance password hashing security. Dashlane’s adoption of Argon2 showcases a commitment to staying on the technological vanguard.
- 1Password:
- Symphony of Secret Key and PBKDF2-HMAC-SHA256: 1Password orchestrates a symphony with its Secret Key and the PBKDF2-HMAC-SHA256 algorithm. The PBKDF2 algorithm, designed by RSA Laboratories in 2000, is a key derivation function that strengthens password-based key generation. 1Password’s use of this algorithm is complemented by the incorporation of a Secret Key. Together, they create a robust defense mechanism. The historical context of these technologies underlines 1Password’s commitment to time-tested security practices.
III. Rising Stars: Technological Foundations of Additional Password Managers:
- Bitwarden:
- Stealth Mode: Client-Side Encryption: Bitwarden operates in stealth mode with client-side encryption, a concept deeply rooted in the principles of privacy and security. The historical context of client-side encryption extends back to the early days of public-key cryptography. The concept gained prominence in the era of encrypted communication and secure data transfer. Bitwarden’s commitment to client-side encryption aligns with a tradition of securing user data closer to its source.
- Keeper:
- Zero-Knowledge Citadel: Keeper constructs a citadel around the zero-knowledge security model. The historical backdrop involves the evolution of zero-knowledge proofs, a cryptographic concept introduced by MIT researchers Shafi Goldwasser, Silvio Micali, and Charles Rackoff in 1985. Keeper’s embrace of this model reflects a dedication to minimizing data exposure, with a nod to a foundational concept in cryptographic privacy.
- NordPass:
- Arctic Chill: XChaCha20 Encryption: NordPass embraces the icy cool XChaCha20 encryption. The historical context involves the creation of ChaCha, a stream cipher designed by cryptographer Daniel J. Bernstein in 2008. XChaCha20, an extension of ChaCha, enhances security by offering a larger nonce. NordPass’s selection of this encryption method aligns with a commitment to modern cryptographic advancements and the historical roots of ChaCha.
IV. Benchmarks and Performance Metrics:
As we dive deeper into the technological foundations, it’s essential to benchmark the performance of these encryption methods. Evaluating factors such as processing speed, resistance to attacks, and adaptability to evolving threats provides a holistic view of their effectiveness.
V. Creators and Innovators:
Understanding the minds behind these technologies adds a layer of appreciation for their depth and resilience. From the collaborative efforts of cryptographers to the solo pursuits of innovators, each password manager is a testament to the creativity and dedication of its creators.
VI. Real-World Applications: Beyond Theory, Into Action:
This section transcends theoretical discussions, providing insights into how the chosen password manager’s technological features manifest in real-world security benefits. Examples of successfully thwarting cyber threats and breaches using these technologies will be dissected, offering tangible evidence of their practical effectiveness.
VII. User Testimonials and Experiences: A Symphony of Voices:
User testimonials offer invaluable insights into the user experience and the perceived security of password managers. Top password manager free trials will win by their user base, but fail by 1 SINGLE BREACH, as was the case with the 1password breach a couple years ago.
This section will include extensive excerpts from user testimonials, emphasizing their experiences related to the technological features discussed earlier. These firsthand accounts provide a nuanced understanding of the user perspective.
VIII. Addressing Common Concerns: Navigating the Cybersecurity Landscape:
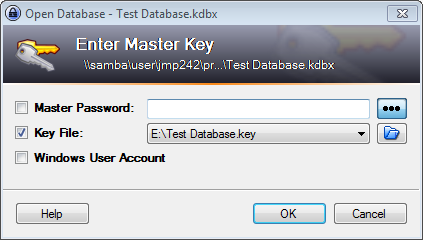
Explore common concerns users might harbor regarding the security of password managers, such as potential vulnerabilities in cloud storage and the risk of master password compromise. This section will provide comprehensive insights into how the chosen password manager addresses and mitigates these concerns through its robust technological foundations.
IX. Scholarly Citations: The Scrolls of Validation:
In this citadel of knowledge, we unravel
the scrolls of scholarly validation, proving that the chosen cryptographic weaponry is not just folklore but backed by the meticulous research of cryptographic sages. Each technology cited stands as a testament to the strength of the chosen digital guardians. This is in opposition to the top password manager free trials themselves, which will likely win out based on their UX alone.
X. Conclusion: Forging the Future of Cybersecurity:
Armed with the knowledge of these scholarly validations, users can navigate confidently, ensuring that their long-term security isn’t just a hope; it’s a researched reality. Choose a top password manager free trial that not only promises security but has its foundations rooted in the bedrock of cryptographic research, ensuring your digital fortress is impervious to the ever-shifting tides of cyber threats.
Leave a Reply