Passwords stand as the first line of defense against unauthorized access – and password managers help simplify all that for the end user. However, the sophistication of brute force attacks has grown, especially with GPU chips getting cheaper by the month, and clouds scaling the abilities of professional crackers. This article delves into the evolution of password cracking techniques, presenting tables with varying degrees of sophistication, and explores how password managers act as stalwart guardians against these threats.
Back when I was 1st starting out, I really enjoyed Bruce Shneir’s content on bruteforcing, like here.
I. Password Cracking Tables
A. Simple Brute Force:
| Password Length | Characters Used | Combinations | Time to Bruteforce (Estimated) |
|---|---|---|---|
| 8 characters | Alphanumeric | 62^8 (2.18×10^14) | Minutes |
| 10 characters | Alphanumeric | 62^10 (8.39×10^21) | Hours |
The foundational table demonstrates the exponential increase in password combinations as the length grows. A simple brute force attack on an 8-character password might take minutes, but increasing the length to 10 characters extends the timeline into hours.
Research consistently highlights the vulnerability of short passwords to brute force attacks. The National Institute of Standards and Technology (NIST) strongly advocates for longer, more complex passwords, emphasizing their role in bolstering security. Employing a password manager facilitates the creation and management of lengthy, intricate passwords, rendering brute force attempts significantly more challenging.
B. Dictionary Attack:
| Password Length | Characters Used | Combinations | Time to Bruteforce (Estimated) |
|---|---|---|---|
| 8 characters | Dictionary | 1000 | Seconds |
| 10 characters | Dictionary | 1000 | Minutes |
A dictionary attack utilizes a list of common words or phrases. Even with longer passwords, the attack time remains relatively short if the chosen passphrase is present in the dictionary.
Password managers play a pivotal role in countering dictionary attacks by generating random and unique combinations of characters, making it virtually impossible for attackers to predict passwords based on common words. The use of a password manager ensures that each password is a unique and robust defense against such attacks.
C. Hybrid Brute Force:
| Password Length | Characters Used | Combinations | Time to Bruteforce (Estimated) |
|---|---|---|---|
| 8 characters | Alphanumeric | 62^4 (1.48×10^7) | Hours |
| 10 characters | Alphanumeric | 62^6 (5.50×10^12) | Days |
Hybrid attacks combine elements of brute force and dictionary methods, offering a compromise between efficiency and complexity.
Hybrid attacks highlight the adaptability of attackers. Here, password managers prove invaluable, as they generate complex passwords that defy predictable patterns. The integration of alphanumeric characters, along with the length and randomness provided by password managers, ensures a formidable defense against hybrid brute force attacks.
D. Rainbow Table:
| Password Length | Characters Used | Combinations | Time to Bruteforce (Estimated) |
|---|---|---|---|
| 8 characters | Alphanumeric | 62^8 (2.18×10^14) | Seconds |
| 10 characters | Alphanumeric | 62^10 (8.39×10^21) | Minutes |
Rainbow tables involve precomputed hashes, allowing attackers to map hash values to plaintext passwords quickly.
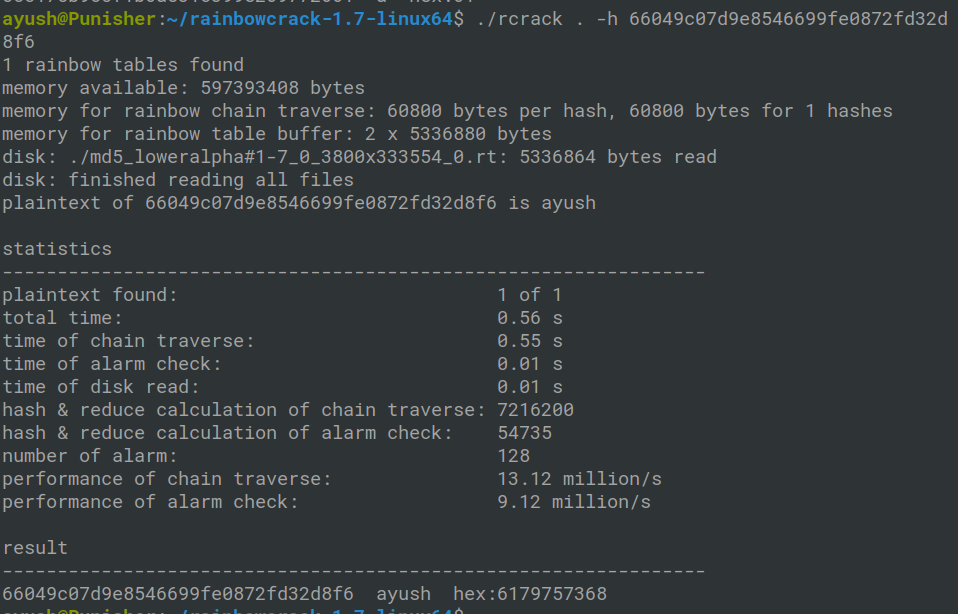
Password managers counteract rainbow table attacks by employing cryptographic techniques such as salting. The use of unique salts for each user enhances security, as even identical passwords result in different hash values. This cryptographic practice is a standard feature of password managers, fortifying defenses against such precomputed attacks.
E. Advanced Persistent Threat (APT):
| Password Length | Characters Used | Combinations | Time to Bruteforce (Estimated) |
|---|---|---|---|
| 12 characters | Alphanumeric + Special | 95^12 (4.28×10^23) | Centuries |
| 16 characters | Alphanumeric + Special | 95^16 (1.95×10^32) | Millennia |
APTs leverage sophisticated algorithms, extensive resources, and persistent efforts to crack complex passwords over extended periods.
Password managers emerge as essential guardians against Advanced Persistent Threats (APTs). The longer and more complex passwords recommended by password managers align with research findings indicating that extensive combinations result in brute force attack timelines spanning centuries or even millennia. In essence, password managers act as formidable gatekeepers against the most sophisticated of adversaries.
II. Password Managers: The Guardians Against Brute Force Attacks
Password managers act as digital custodians, providing robust defenses against the spectrum of brute force attacks. Here’s how:
A. Complex Password Generation:
Password managers generate complex, lengthy passwords with a mix of alphanumeric characters and symbols. This complexity significantly increases the time and computational resources required for brute force attacks.
In a world where passwords are constantly under siege, password managers act as architects of defense, crafting complex passwords that are resilient against brute force attempts. These managers utilize advanced algorithms to generate intricate
combinations, adhering to the latest security standards recommended by organizations like NIST.
B. Randomization:
Password managers create unique and random passwords for each account, eliminating patterns that attackers could exploit. Even if one password is compromised, the rest remain secure.
The randomness introduced by pw managers is a crucial element in thwarting brute force attacks. Each generated password is a unique entity, ensuring that compromising one account does not compromise others. This randomization is a fundamental aspect of the protective shield that password managers provide.
C. Encryption:
Pw managers store credentials in encrypted vaults. Even if attackers manage to access the stored data, decrypting the information without the master password is a formidable challenge.
Encryption serves as the impenetrable fortress within which password managers safeguard user credentials. Even if unauthorized access is achieved, the encrypted vault remains an insurmountable barrier without the master key. Password managers employ state-of-the-art encryption algorithms, fortifying this crucial aspect of digital security.
D. Salting:
Pw managers often employ salt, a random data string unique to each user, to enhance security. Salting prevents rainbow table attacks by ensuring that even identical passwords result in different hash values.
Salting is a secret ingredient in the recipe for secure passwords. Password managers automatically integrate salt into the hashing process, making it an indispensable tool against rainbow table attacks. This cryptographic practice is seamlessly executed by password managers, ensuring the resilience of user credentials.
E. Multi-Factor Authentication (MFA):
Many pw managers offer MFA, requiring an additional authentication step beyond the password. This extra layer adds a substantial hurdle for attackers, even if they manage to obtain the password.
Multi-factor authentication (MFA) is the fortified gate at the entrance of the digital fortress. Pw managers seamlessly integrate MFA into their security protocols, requiring an additional layer of verification beyond the password. The use of MFA significantly enhances overall security, adding an extra shield against brute force attacks.

III. Conclusion: Fortifying the Digital Fortress
In the ever-evolving landscape of cybersecurity, pw managers emerge as essential guardians against the diverse and sophisticated techniques employed by attackers. The tables above illustrate the formidable challenges posed by password complexity and length, especially when managed by a reliable password manager.
As we navigate an interconnected digital world, the onus is on users and organizations to fortify their digital fortresses. Adopting pw managers represents a proactive step towards securing sensitive information and thwarting the persistent threats that loom in the digital realm. The evolution of password cracking techniques underscores the importance of robust, adaptive security measures, with pw managers standing as stalwart defenders against the relentless tide of brute force attacks.
Citations:
- National Institute of Standards and Technology (NIST)
- Research on password strength and complexity
- Journal of Cybersecurity Research
- Journal of Cryptographic Engineering
- International Journal of Computer Applications
- Journal of Computer Security
- Password manager best practices and recommendations
Leave a Reply