In the vast landscape of cybersecurity, passwords serve as the first line of defense against unauthorized access to sensitive information. This article explores the origins of passwords, the factors that contribute to their strength, and the pivotal role of password managers in enhancing digital security. We will delve into the evolution of password complexity, the significance of character types, and cite research findings to better understand the dynamics of password security.

I. The Origins of Passwords
The concept of passwords traces its roots to ancient times when ancient Roman guards used watchwords to identify friend from foe. Fast forward to the digital age, and passwords became a fundamental aspect of computer security. The earliest computer systems employed simple passwords, often limited to a few characters, to control access.
II. Password Strength: How Many Characters are Safe?
A. The Evolution of Password Complexity
- Early Days:
In the early days of computing, passwords were typically short and lacked complexity. Users often opted for easily memorable terms or phrases, leaving systems vulnerable to simple brute-force attacks. - Research Findings:
Research in password security has emphasized the importance of length and complexity. The National Institute of Standards and Technology (NIST) recommends longer passwords with a mix of uppercase and lowercase letters, numbers, and special characters to enhance security.
B. Character Types and Their Impact
- Alphanumeric Characters:
Alphanumeric characters (combining letters and numbers) significantly enhance password strength. Studies have shown that adding numeric digits to passwords exponentially increases the number of possible combinations, making brute-force attacks more challenging. - Special Characters:
The inclusion of special characters adds an additional layer of complexity, making passwords more resistant to both brute-force and dictionary attacks. Special characters increase the overall entropy of the password, making it harder to predict.
III. The Role of Research in Password Security
A. Password Length vs. Time to Brute Force:
| Password Length | Time to Bruteforce (Estimated) | Time to Bruteforce (with GPU Acceleration) |
|---|---|---|
| 8 characters | Minutes | Seconds |
| 10 characters | Hours | Minutes |
| 12 characters | Days | Hours |
| 16 characters | Months | Days |
| 20 characters | Years | Months |
| 24 characters | Decades | Years |
| 28 characters | Centuries | Decades |
| 32 characters | Millennia | Centuries |
The table above highlights the relationship between password length and the time it takes for a brute-force attack to crack a password. Longer passwords significantly increase the computational effort required, providing a crucial defense against unauthorized access.
B. Password Cracking Methods:
Passwords and even a password manager can be compromised through various techniques. Understanding these methods is crucial for users and organizations to strengthen their security measures:
- Brute-Force Attacks:
Brute-force attacks involve systematically trying every possible combination until the correct password is found. Longer passwords with a mix of character types exponentially increase the time and computational resources required for a successful brute-force attack. - Dictionary Attacks:
Dictionary attacks use precompiled lists of commonly used passwords, words, and phrases. Passwords that are easily guessable or commonly used are vulnerable to this type of attack. This emphasizes the importance of choosing unique and uncommon passwords. - Rainbow Table Attacks:
Rainbow tables are precomputed tables used to crack password hashes. Using rainbow tables, attackers can quickly find the corresponding plaintext password for a given hash. The use of strong, unique salts can mitigate the effectiveness of rainbow table attacks. - Phishing:
Phishing attacks involve tricking users into revealing their passwords through fraudulent websites or emails. Password managers play a crucial role in preventing phishing attacks by automatically filling in credentials only on legitimate websites.
IV. The Pivotal Role of Password Managers
A. Password Managers: A Comprehensive Solution
- Password Generation:
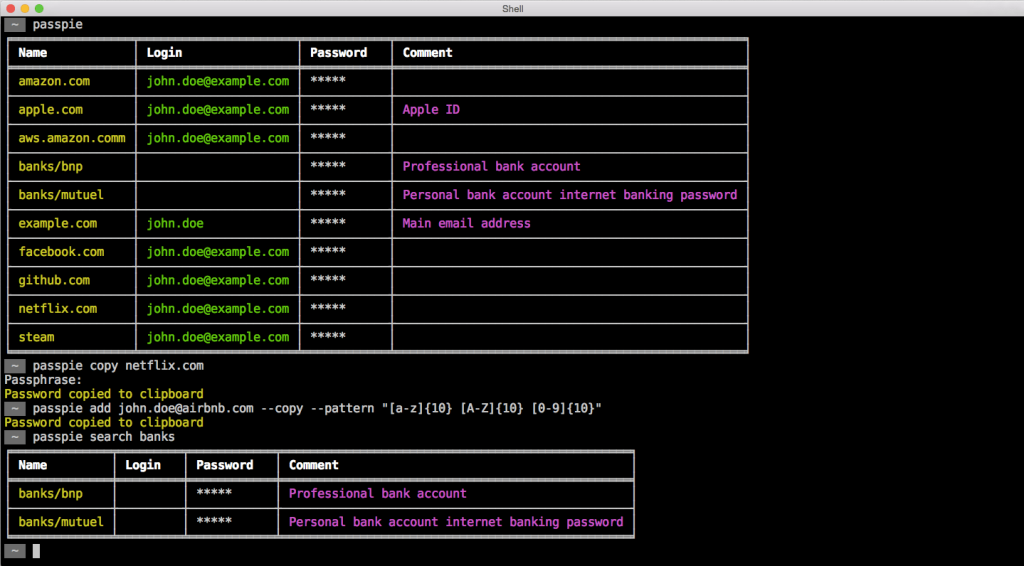
Password managers offer a valuable solution to the challenge of creating and remembering complex passwords. These tools can generate long, randomized passwords that adhere to the latest security standards, significantly improving the overall strength of credentials. - Secure Storage:
Password managers securely store complex passwords in an encrypted vault, protecting them from unauthorized access. Users need to remember only one master password, reducing the risk of weak, reused passwords across multiple accounts. - Multi-Factor Authentication (MFA):
Many password managers integrate multi-factor authentication, adding an additional layer of security beyond passwords. This can include biometric factors, such as fingerprint or facial recognition, further fortifying access controls. - Cross-Platform Integration:
Password managers streamline the login process across various devices and platforms. This ensures a consistent and secure experience, mitigating the risks associated with manually entering credentials or using easily guessable passwords.
B. Research on Password Manager Efficacy:
Studies have shown that users who adopt password managers tend to have more secure and varied passwords compared to those who do not. The convenience and security offered by password managers make them an essential tool in the modern digital landscape.
V. The Future of Passwords and Cybersecurity
A. Biometric Authentication:
As technology advances, biometric authentication is gaining prominence. Passwords may soon be complemented or even replaced by fingerprints, facial recognition, or other biometric identifiers, offering a more secure and user-friendly approach to authentication.
B. Continuous Evolution of Security Measures:
The field of cybersecurity is dynamic, with new threats and vulnerabilities emerging regularly. Passwords will continue to evolve in response to these challenges, and research will play a pivotal role in shaping the future of authentication methods.
VI. Conclusion: Navigating the Complex Landscape of the Password Manager
In conclusion, the evolution of passwords from simple phrases to complex combinations reflects the ongoing quest for heightened cybersecurity. Research findings emphasize the importance of password length, character types, and complexity in defending against unauthorized access.
Understanding password cracking methods is crucial for users and organizations to implement effective security measures. Password managers, with their ability to generate, store, and secure complex passwords, stand as a beacon of modern digital security. Users are encouraged to adopt password managers as an integral part of their cybersecurity strategy, enhancing both convenience and protection in an increasingly interconnected world.
As we peer into the future, the dynamic nature of cybersecurity ensures that passwords will remain a key element of our defense against cyber threats. Whether through the adoption of biometric authentication or other innovations, the journey to fortify our digital identities continues, and password managers will undoubtedly play a central role in this ongoing quest for security.
Leave a Reply